After the long-winding road of discussion and deliberation, revision, disagreements and adjustments, the Open Web Application Security Project (OWASP) are updating their venerable Top 10 list of the most critical web application security risks since 2013. This update brings with it three new entries to the list, based on data OWASP collected and analyzed. Here’s all you need to know about OWASP Top 10 2017.
With new attacks and a change of landscape since 2013, many would agree that the OWASP Top 10 has been due for an update for some time now. However, with the Top 10 relied-on extensively by thousands of professionals and organizations for their vulnerability and security education programmes, changes are bound to be contentious.
The first Release Candidate (RC) was met with quite some push-back from the application security community, which compelled the OWASP Top 10 project to go back to the drawing-board and refine the proposed list based on the community’s feedback.
What’s new?
The OWASP Top 10 introduced three new web application security risks — XML external entities (XXE), insecure deserialization and insufficient logging and monitoring. This post will focus at these new category of vulnerabilities.
XML External Entities (XXE)
XML External Entities (XXE), at number four on the list, is probably one of the most awaited vulnerability classes to make it’s debut on the OWASP Top 10 list. XXE refers to a class of web application vulnerabilities that allows an attacker to conduct Server-side Request Forgery (SSRF) attacks by abusing widely available, but rarely used features in XML parsers called external entities.
A successful attack could allow an attacker to extract data as well as forge remote request from
the server where the vulnerable XML parser is being exploited. This means that an attacker could be able to scan internal systems, perform denial-of-service (DoS) attacks, as well as escalate this to other attacks.
Insecure Deserialization
At number 8 on the OWASP Top 10 list, insecure deserialization would allow an attacker to remotely execute code within a vulnerable application. While successful exploitation of insecure deserialization in vulnerable web applications is not for faint-hearted attackers, if successful, an attacker can escalate an insecure deserialization attack by elevating privileges on the server running the vulnerable web application. From there, an attacker can pivot throughout the internal network and further escalate attacks.
While in the past few years Java applications have stolen the spotlight when it comes to insecure deserialization, Java applications are certainly not alone here, with similar attacks possible in many other applications including PHP, ASP.NET and Python based web applications.
Insufficient Logging and Monitoring
The final entry in the OWASP Top 10 2017 is a rather, interesting one. Insufficient logging and monitoring is a prevalent issue in many web applications and it deals primarily with situations where a deployed web application is either not properly logging and/or monitoring events that typically relate to an attacker probing for vulnerabilities.
A typical example of this is when an attacker can make requests to an authentication system without any rate-limit. In such an event where the application not only allows an attacker to make virtually unlimited requests to guess a user’s credentials, insufficient logging and/or monitoring could cause an attacker to pull off an attack without an application administrator having any clue that the application is in-fact under attack.
It’s important to note that this category tends to refer more to a set of lack of best practices that could hinder detection and response to an attack, rather that it being a web application vulnerability.
What else has changed?
Since space is limited, the OWASP Top 10 project opted to either drop some risks that were no longer as important or prevalent. In other cases, risks from the 2013 Top 10 were merged together. Additionally, since the OWASP Top 10 is ordered by prevalence of risk, some risks have moved rank.
Cross-site request forgery (CSRF) and unvalidated redirects and forwards, number eight and number ten respectively in OWASP Top 10 2013, have been dropped. This is not to say that these two vulnerabilities are no longer important to keep in mind as defenders. Furthermore, the Top 10 2017 merges 2013’s insecure direct object references (IDOR) and missing function level access control into the broken access control at position number five.
| OWASP Top 10 2013 | OWASP Top 10 2017 |
|---|---|
| A1 Injection | A1 Injection |
| A2 Broken Authentication and Session Management | A2 Broken Authentication and Session Management |
| A3 Cross-site Scripting (XSS) | A3 Sensitive Data Exposure |
| A4 Insecure Direct Object References | A4 XML External Entities (XXE) — New |
| A5 Security Misconfiguration | A5 Broken Access Control — Merged |
| A6 Sensitive Data Exposure | A6 Security Misconfiguration |
| A7 Missing Function Level Access Control | A7 Cross-Site Scripting |
| A8 Cross-Site Request Forgery (CSRF) — Removed | A8 Insecure Deserialization — New |
| A9 Using Components with Known Vulnerabilities | A9 Using Components with Known Vulnerabilities |
| A10 Unvalidated Redirects and Forwards — Removed | A10 Insufficient Logging and Monitoring — New |
OWASP Top 10 2017 Reports in Acunetix
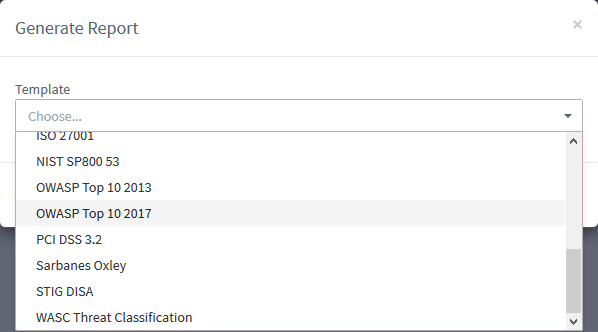
Generating OWASP Top 10 2017 reports in Acunetix is now possible as of build 11.0.173271618 released on 24th November 2017. Please refer to the Generating Reports help article for more information about how to generate reports in Acunetix.
Producing a prioritized list of 10 application security threats is not only incredibly difficult, but it is unreasonable to expect nothing to be left behind. To such an extent, the OWASP Top 10 is not intended ‘one list to rule them all’. Instead, it serves as a great starting and reference point for web application security programs and web security education — a legacy which the Top 10 2017 list continues.
Get the latest content on web security
in your inbox each week.





